Our 2026 Women in Business report explores the mid-market’s commitment to DE&I and gender diversity in leadership and the impact this has on business success.


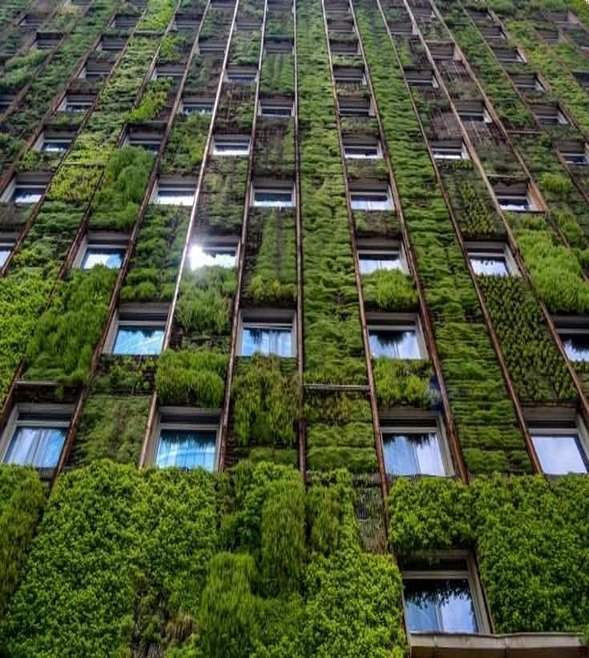
Mid-market firms are scaling sustainability for growth, not just compliance. Grant Thornton’s International Business Report (IBR) 2025 report reveals how sustainability investments are driving profitability, resilience and global expansion — despite regulatory shifts and political uncertainty.

Instability has come to define the global business landscape and the ability for mid-market firms to thrive through disruption is becoming a key differentiator.
The EU Council approves Directive on the simplification of sustainability reporting and due diligence requirements.

Our 2026 Women in Business report explores the mid-market’s commitment to DE&I and gender diversity in leadership and the impact this has on business success.

The first article in our new Insights into IFRS 18 series aims to provide a snapshot of the new requirements of IFRS 18 for entities applying IFRS Accounting Standards.

This update aims to summarise the key changes to European sustainability reporting, and the implications for entities preparing sustainability reports in 2026.

The 2026 edition of our annual Navigating the Changes to IFRS publication has been released. It includes changes to IFRS Accounting Standards issued in the past year

The EU Council and Parliament reach an agreement that furthers progress toward the simplification of sustainability reporting and due diligence requirements.

The ISSB has amended IFRS S2 to provide targeted reliefs for companies when calculating and disclosing their greenhouse gas emissions.

The European Financial Reporting Advisory Group issues technical advice to the European Commission on revising the European Sustainability Reporting Standards.

While return-to-office mandates continue to gather pace, remote working remains a common arrangement for companies with global workforces. These arrangements have historically posed concern that the individual’s presence in another country could create corporate tax exposure for the employing country, creating a permanent establishment.

The EU Parliament has made further progress on its position regarding proposed Omnibus changes to the CSRD and CSDDD.

Employing remote workers in Poland does not necessarily create a permanent establishment in Poland (PE) – this has been confirmed by the Polish Supreme Administrative Court (NSA) in its recent judgment of 28 October 2025

Our detailed year-end payroll checklist provides a structured framework for reconciling data, validating employee records, processing final payouts and meeting federal, state and local filing deadlines.

Instability has come to define the global business landscape and the ability for mid-market firms to thrive through disruption is becoming a key differentiator.

This Insight covers the accounting for share-based payment transactions with non-employees.
The EU Parliament continues negotiations on its position regarding proposed Omnibus changes to the CSRD and CSDDD.

We have released 'IFRS Example Consolidated Financial Statements 2025' (Example Financial Statements) to support member firms' commitment to high-quality, consistent application of IFRS. The Example Financial Statements illustrate a twelve-month accounting period beginning on 1 January 2025.